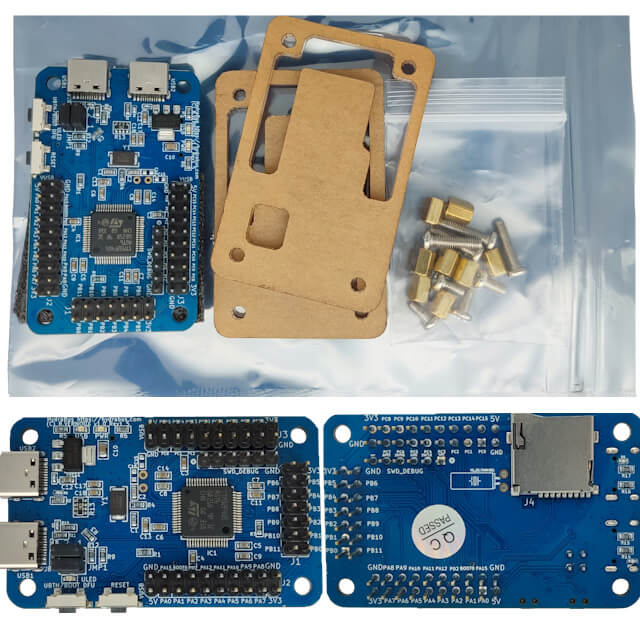
We are excited to announce that after a long wait, primarily due to the global chip shortage, the new kit HydraBus v1.0 Rev1.5 + HydraNFC Shield v2 R1.5 are now in stock!
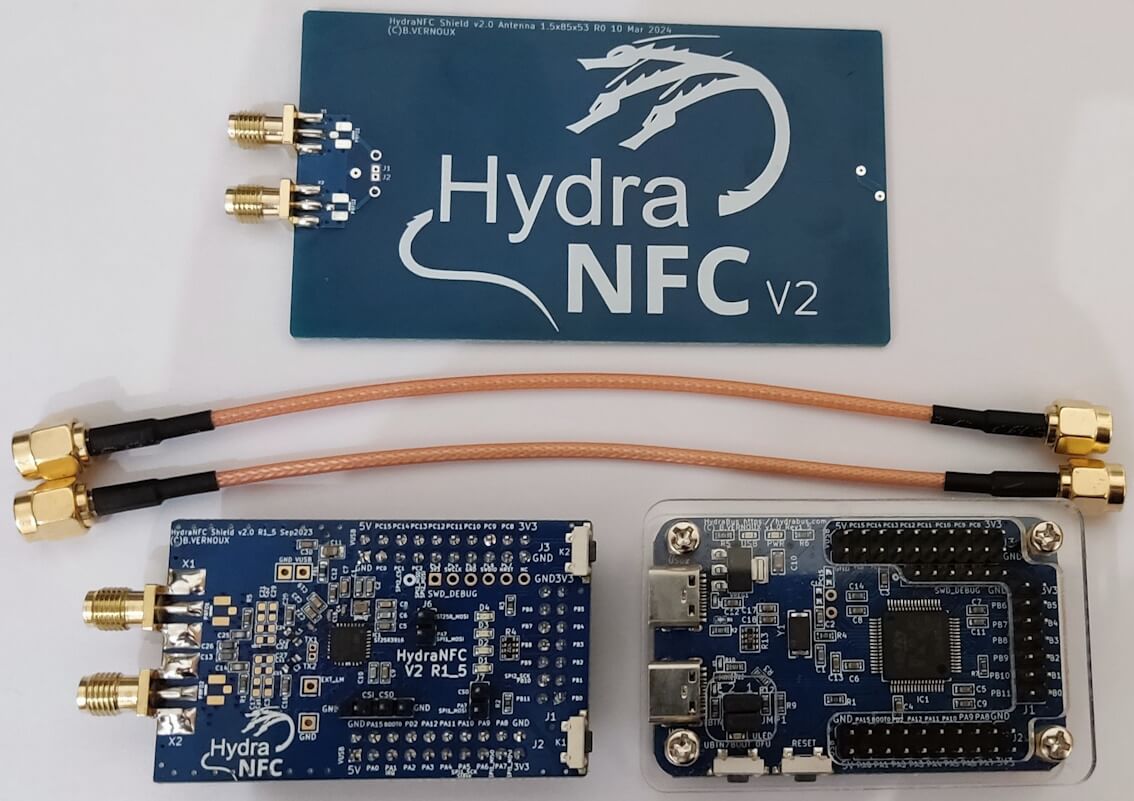
These updated versions come with enhanced features and improvements, ensuring better performance and reliability for your projects.
Key Highlights:
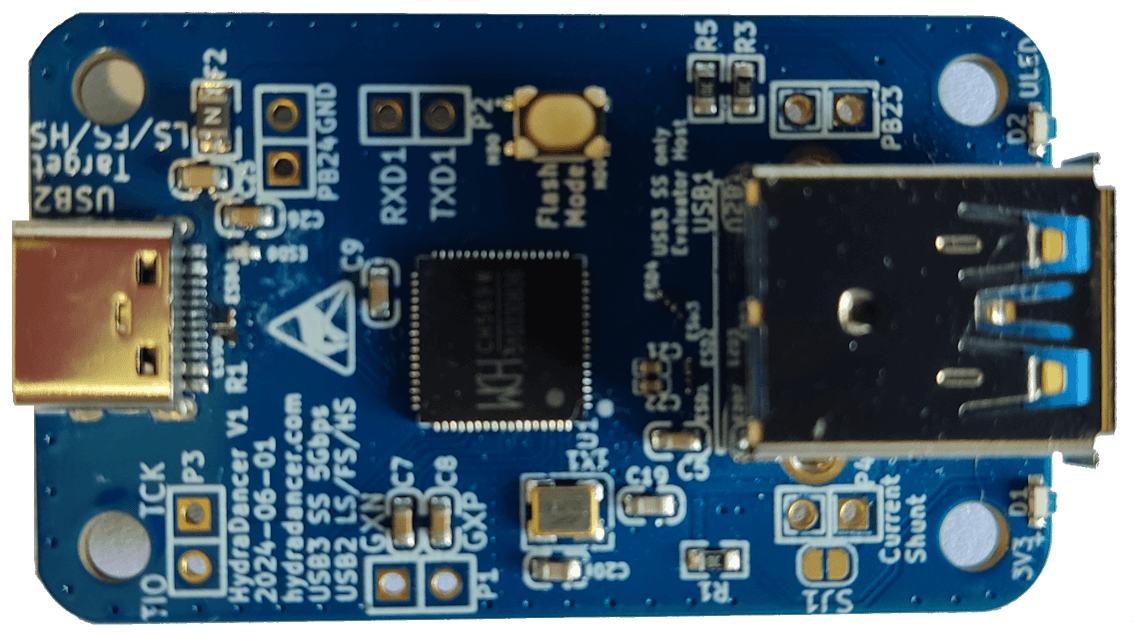
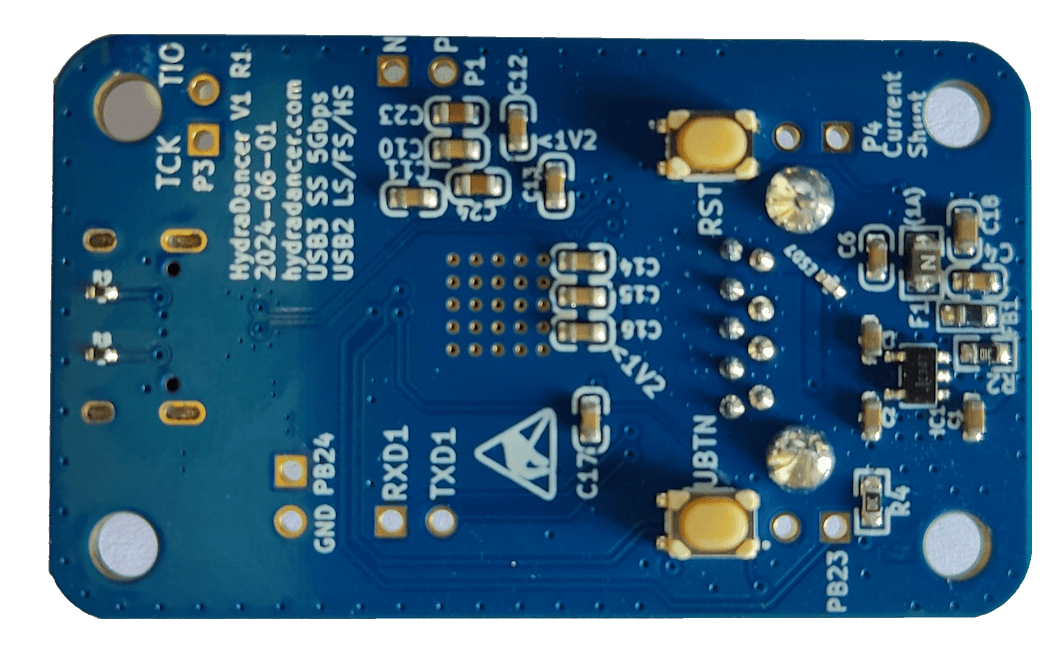
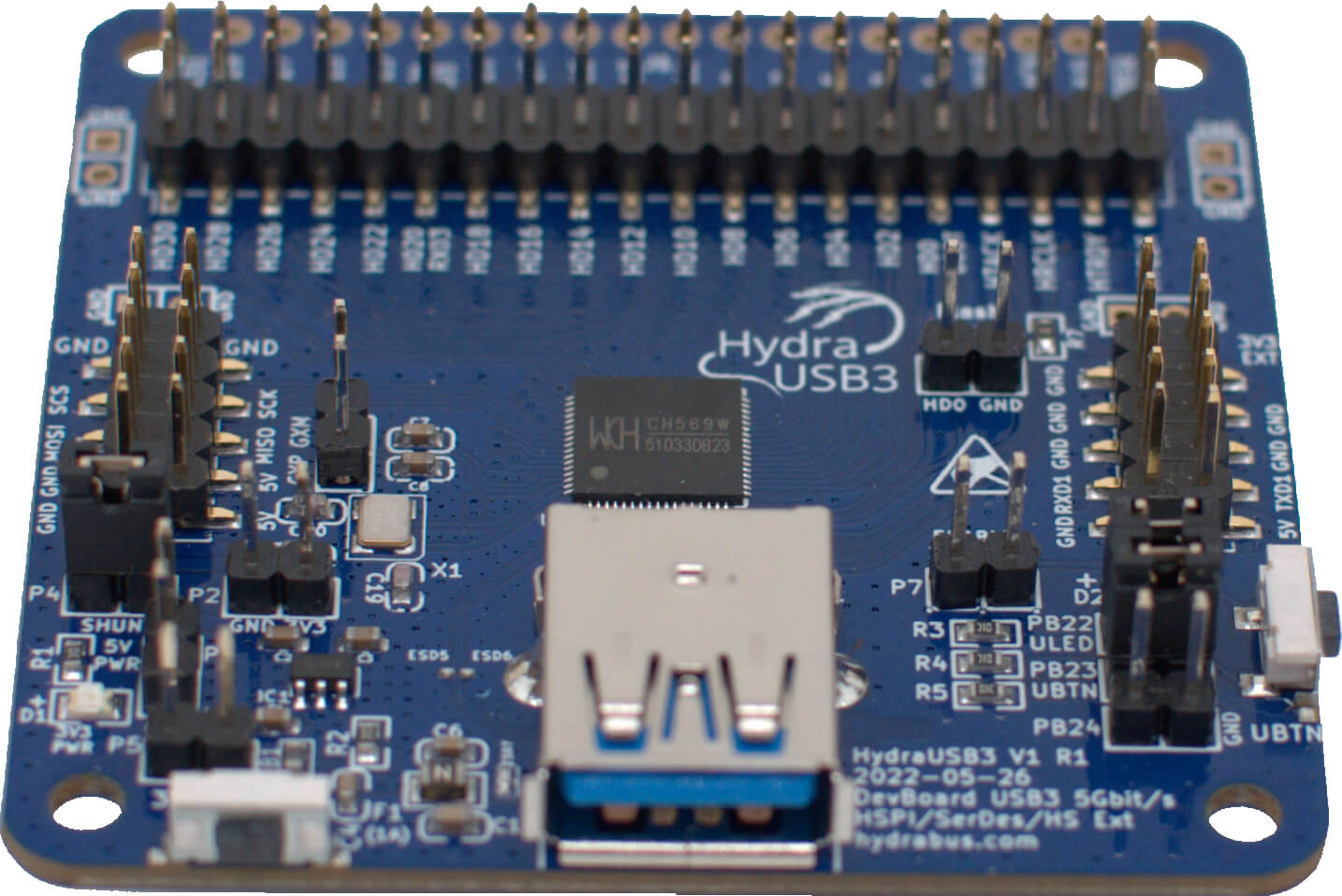
- HydraBus v1.0 Rev1.5: Improved design (with USB-C) for better functionality and ease of use.
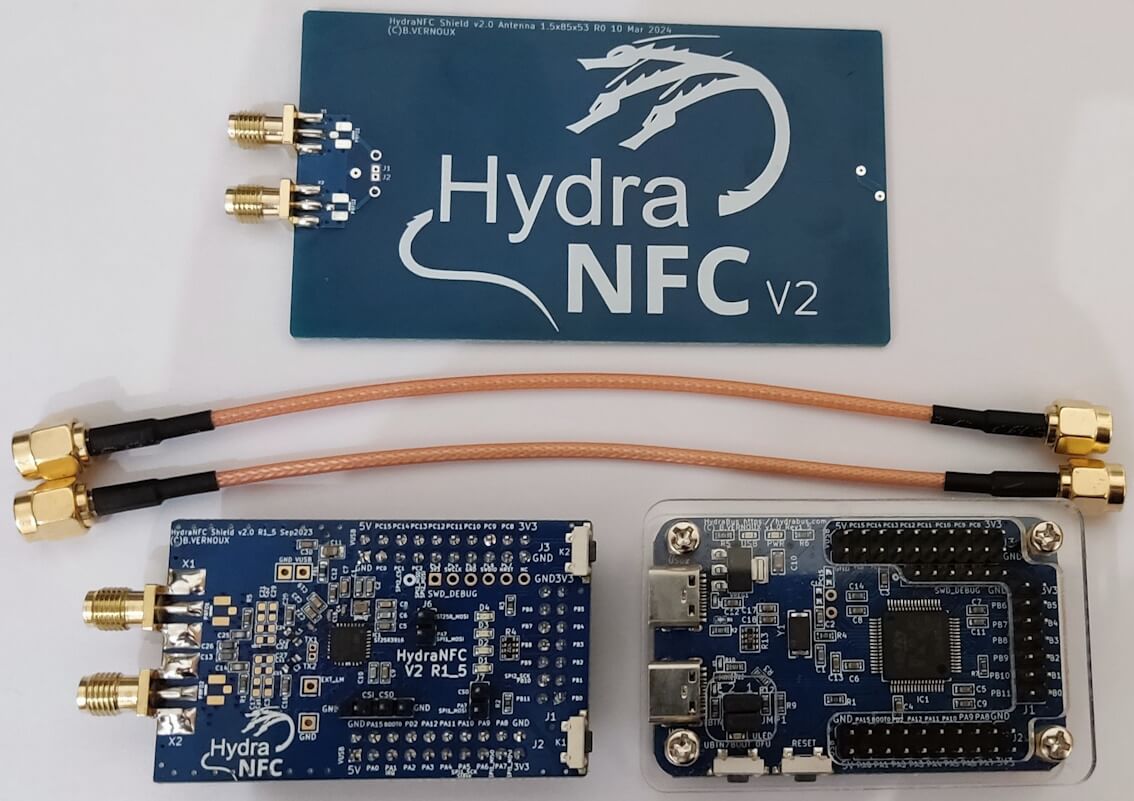
- HydraNFC Shield v2 R1.5: Enhanced Tuning and performance with the latest standards in NFC technology.
Thank you for your patience and continued support. Get your hands on the latest versions today and take your projects to the next level!
https://hydrabus.com/product/hydrabus-v1-0-rev1-5-hydranfc-shield-v2-r1-5